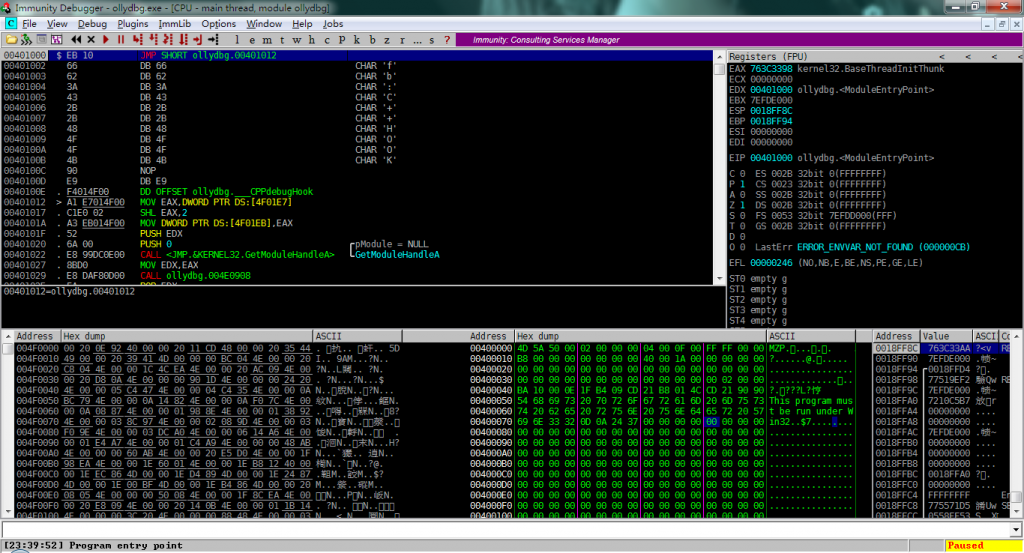
IDA对Unicode的处理不能说很烂,但是有的时候却比较蛋疼。例如神马中文之类的,但是除此之外,对于英文的字符串处理在部分地方也是有问题的,例如上面的内容。
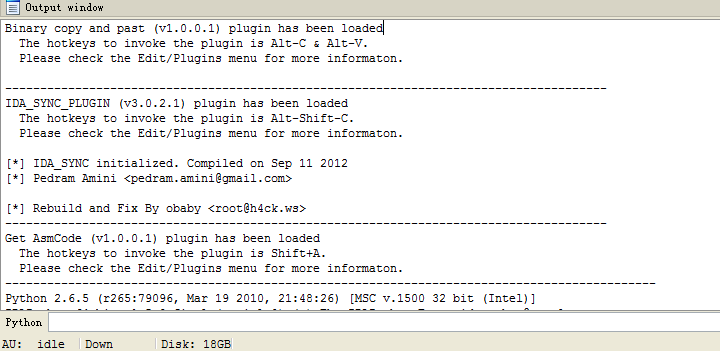
同样在idb刚创建的时候对于unicode字符串的解析也存在问题,例如下面的内容:
真正的字符串内容应该是ReadFromRegistry。但是ida很蛋疼的把第一个R当作dw给处理掉了,于是剩下了一个眉头的身子。
在创建string之后默认是采用的当前idb数据库的字符串格式,如果想要创建正确的字符串需要用到SetAsciiStyle(http://www.hex-rays.com/products/ida/support/idadoc/613.shtml)。